Tryhackme friday overtime – Challenge overview
Tryhackme Friday Overtime challenge is a simulation task. In it, you become a CTI (Cyber Threat Intelligence*) Analyst and have to analyse malware based on real-world cyberattack. To accomplish this, I interacted with malware samples in the virtual machine (VM), which acts as isolated environment.
Note: In order to launch a VM and ,consequently, to complete the task, you must be a premium user on the Tryhackme platform.
* Cyber Threat Intelligence is evidence-based knowledge about adversaries, including their indicators, tactics, motivations, and actionable advice against them (definition from tryhackme platform)
Before I begin…
Feel free to jump to a question that you find interesting.
Table of content:
Q1: Who shared the malware samples?
Q2: What is the SHA1 hash of the file “pRsm.dll” inside samples.zip?
Q3: Which malware framework utilizes these DLLs as add-on modules?
Q4: Which MITRE ATT&CK Technique is linked to using pRsm.dll in this malware framework?
Q5: What is the CyberChef defanged URL of the malicious download location first seen on 2020-11-02?
Treat this article as a helpful walkthrough for the challenge. I’m not going to just give you the answers – after all, where would be fun and value in it? Instead, I will demonstrate how to find the answers to each question, but ultimately, YOU will have to do the work. Have fun and let’s begin Tryhackme Friday Overtime 🙂
Q1: Who shared the malware samples?
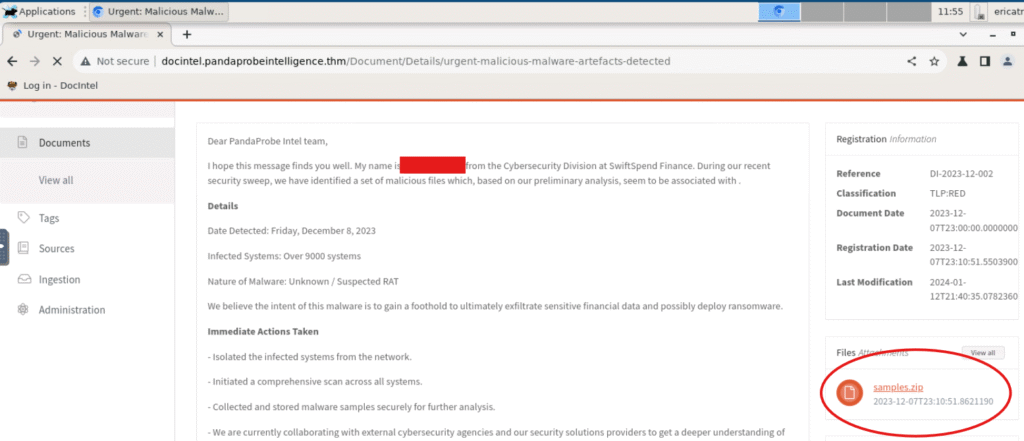
Once you log into the account provided in the task, you will be redirected into main dashboard. From there, you’ll see an email titled “Urgent: Malicious Malware Artefacts Detected” by SwiftSpend Finance. To proceed, click on it to view its full message.
As the question suggests, we are looking for the sender of the attached malware samples (samples.zip are visible on the right). The sender is not an organization, but an individual. (Check out image below)
Q2: What is the SHA1 hash of the file “pRsm.dll” inside samples.zip?
After downloading “samples.zip” (check out image above), we need to unzip it. Open the terminal (in the top left corner “Applications > Terminal emulator”) and use the command:
unzip ./Downloads/smaples.zip // optionally -d <directory name> to extract files into a specific folder. Though in this case, ut's not necessary.Next, the system will ask for a password, which you can find in the email.
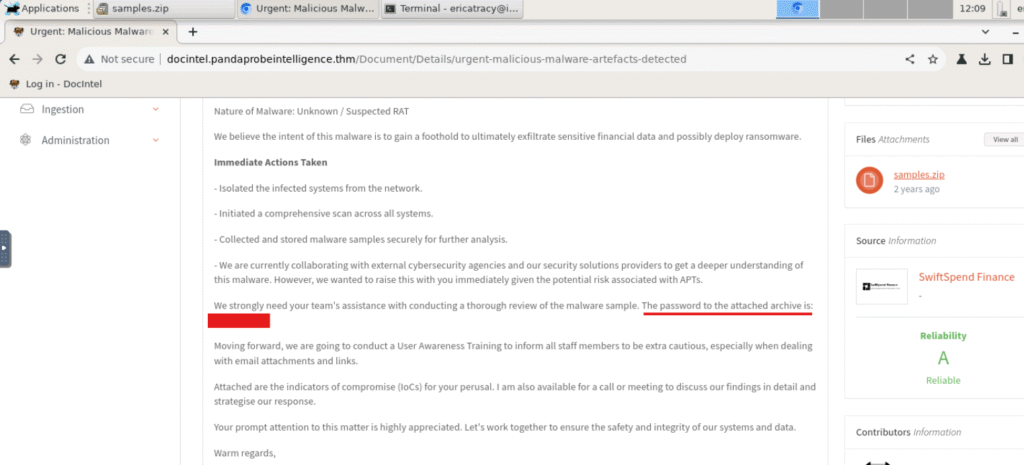
To answer the question, compute SHA1 hash of the file “pRsm.dll” using:
sha1sum pRsm.dll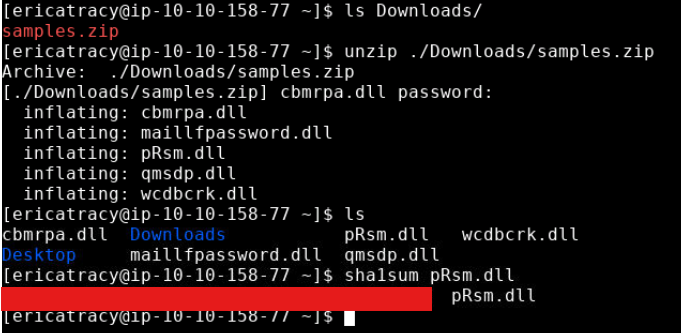
Note: in Linux there are many commands to calculate particular hash. The structure is usually like :<hash_algorithm>sum e.g. sha256sum, md5sum etc.
Q3: Which malware framework utilizes these DLLs as add-on modules?
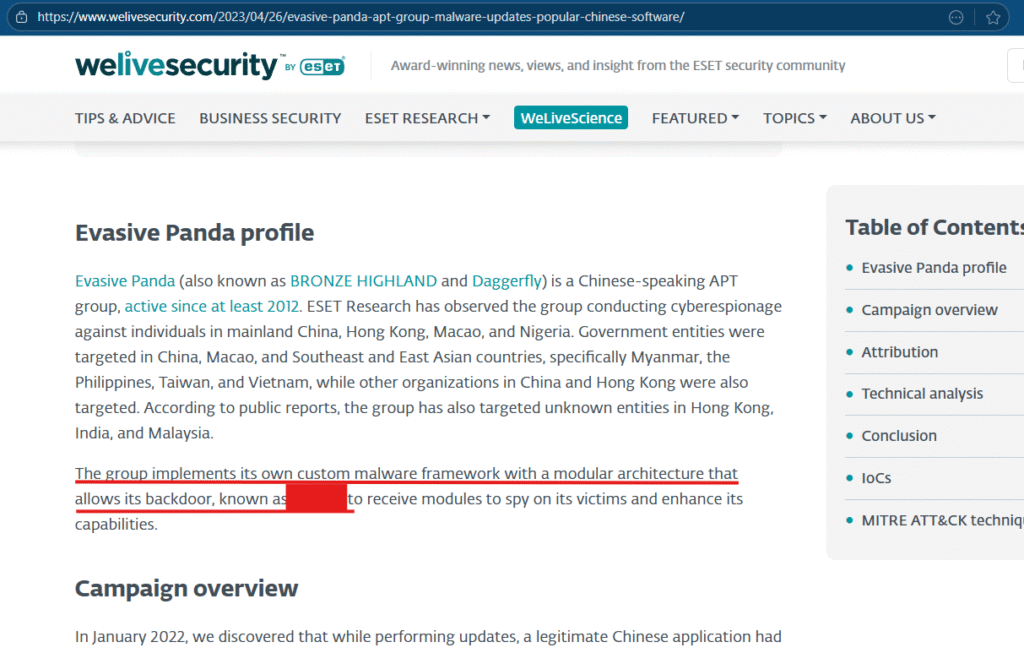
For this one we need to access internet from our own computer (remember the VM is isolated and the whole task is based on real-world cyber-attack). A quick search for “pRsm.dll malware” should lead you to an article on “welivesecurity” titled “Evasive Panda APT group delivers malware via updates for popular Chinese software“.
While reading/scanning through that article you should spot the answer to the question.
Q4: Which MITRE ATT&CK Technique is linked to using pRsm.dll in this malware framework?
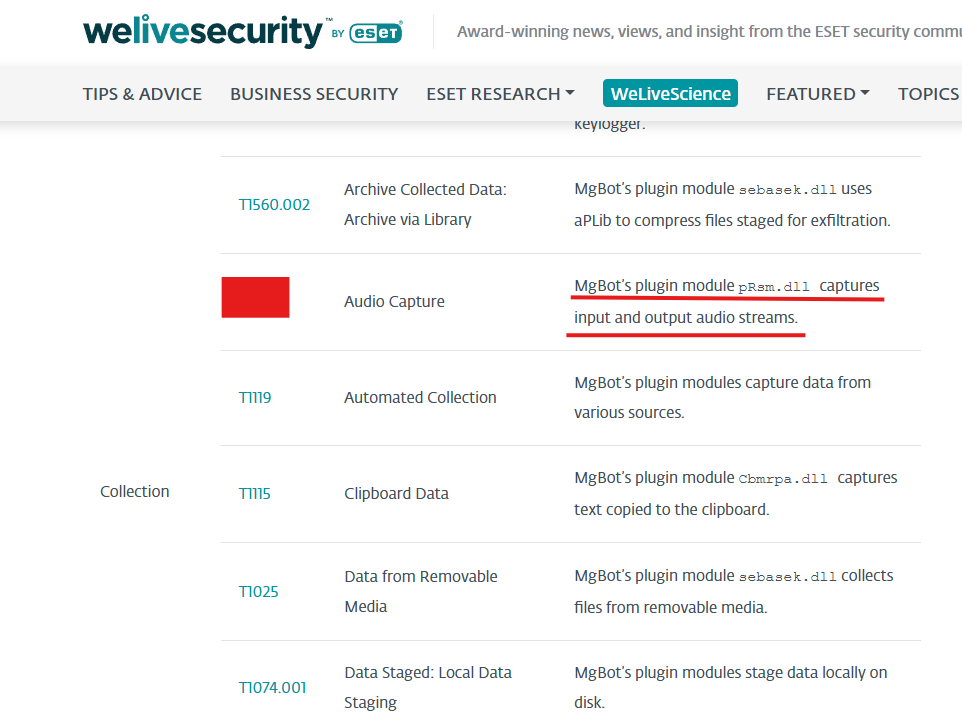
We are still working with article titled “Evasive Panda APT group delivers malware via updates for popular Chinese software” published on “Welivesecurity”. Because this article is a report on a cyberattack, it naturally includes analysis of the incident – specifically using the MITRE ATT&CK Technique ( Adversarial Tactics, Techniques, and Common Knowledge framework developed by research and development non-profit organization MITRE )
As you continue reading, you will find a section labeled “MITRE ATT&CK techniques” with a table outlining various tactics. To answer the question, simply locate technique code associated with the “pRsm.dll” file.
Q5: What is the CyberChef defanged URL of the malicious download location first seen on 2020-11-02?
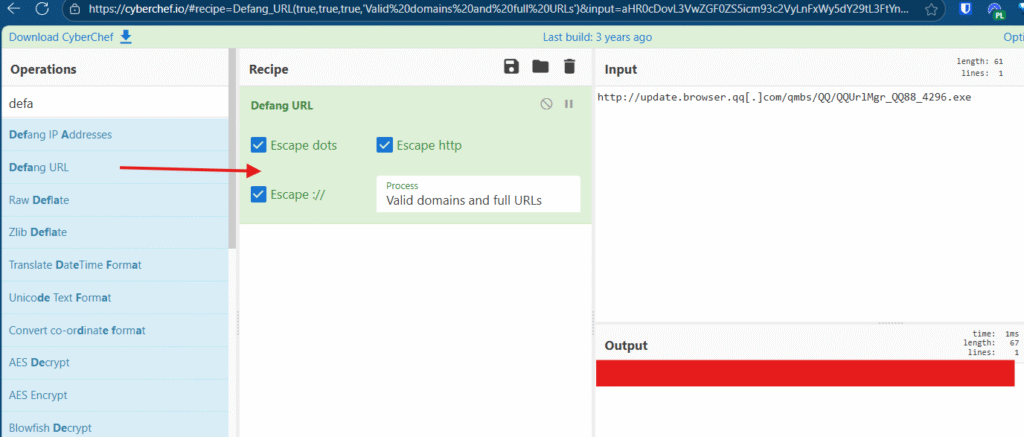
We are still working with article titled “Evasive Panda APT group delivers malware via updates for popular Chinese software” published on “Welivesecurity”. In the section “Technical analysis” section, you will find a URL that matches the date in the question.
Once you have copied the URL, head over to CyberChef – a free online tool to analyse data used by cybersecurity professionals and enthusiasts.
To begin, search for “Defang URL” operation and drag it to a “Recipe” section. Next, paste the URL from the article into the input field. Finally, run the operation to get the result.
Q6: What is the CyberChef defanged IP address of the C&C server first detected on 2020-09-14 using these modules?
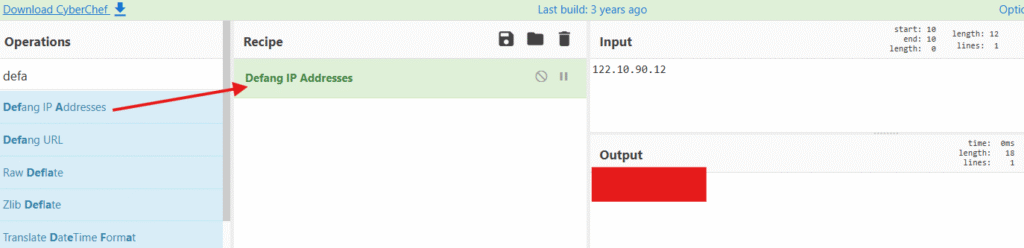
We are still working with article titled “Evasive Panda APT group delivers malware via updates for popular Chinese software” published on “Welivesecurity”. In the “Network” section, you will find an IP address of command and control server (C&C), which matches exact date as in the question.
Once you have located the IP address, open CyberChef – same free online tool we used earlier. To continue, search for “Defang IP address” operation and drag it into “Recipe” ssection. Then, paste the IP address into the input field and run operation to get the result.
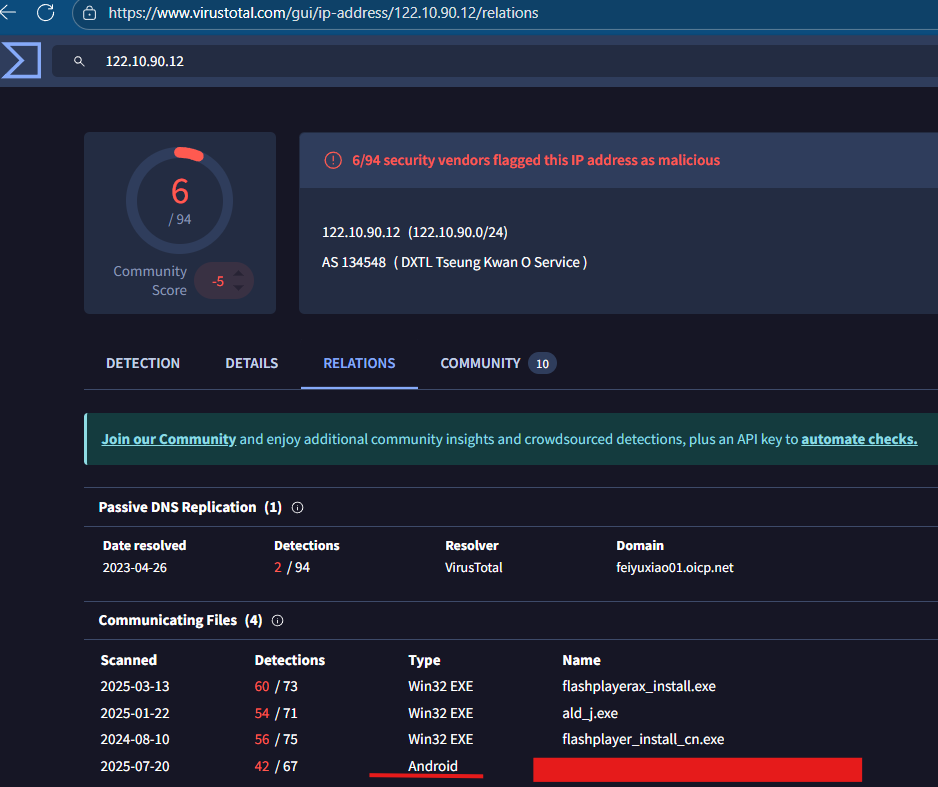
Q7: What is the md5 hash of the spyagent family spyware hosted on the same IP targeting Android devices in Jun 2025?
To answer this question, we need to use the IP address from Q6 and head to the VirusTotal – a platform analyzes data for known malware.
Start by searching for IP address in VirusTotal’s search bar. The default dashboard will show scan results from various antivirus software. To find the answer, go to the “Relations” section. Once there, look for a hash file targeting Android devices with date that matches the one in the question.
Tryhackme Friday Overtime -Conclusion
The Tryhackme Friday Overtime challenge did require some Linux command knowledge. However, more importantly, it tested ability to research like a CTI Analyst. I hope you find this write-up helpful and enjoyed the task of being CTI Anaylst.

